Last updated: November 30, 2025
Best Cloaking helps advertisers and agencies protect campaigns with traffic filtering, bot/VPN detection, and rule-based routing — while complying with applicable platform policies and laws. This documentation covers quickstart, API, SDKs, dashboard setup, and best practices.
Open the dashboard and create your account.
Check your inbox for our verification message and click the link to activate your account.
New accounts start with a 7-day trial that includes 1 Flow. This lets you build and test a complete setup.
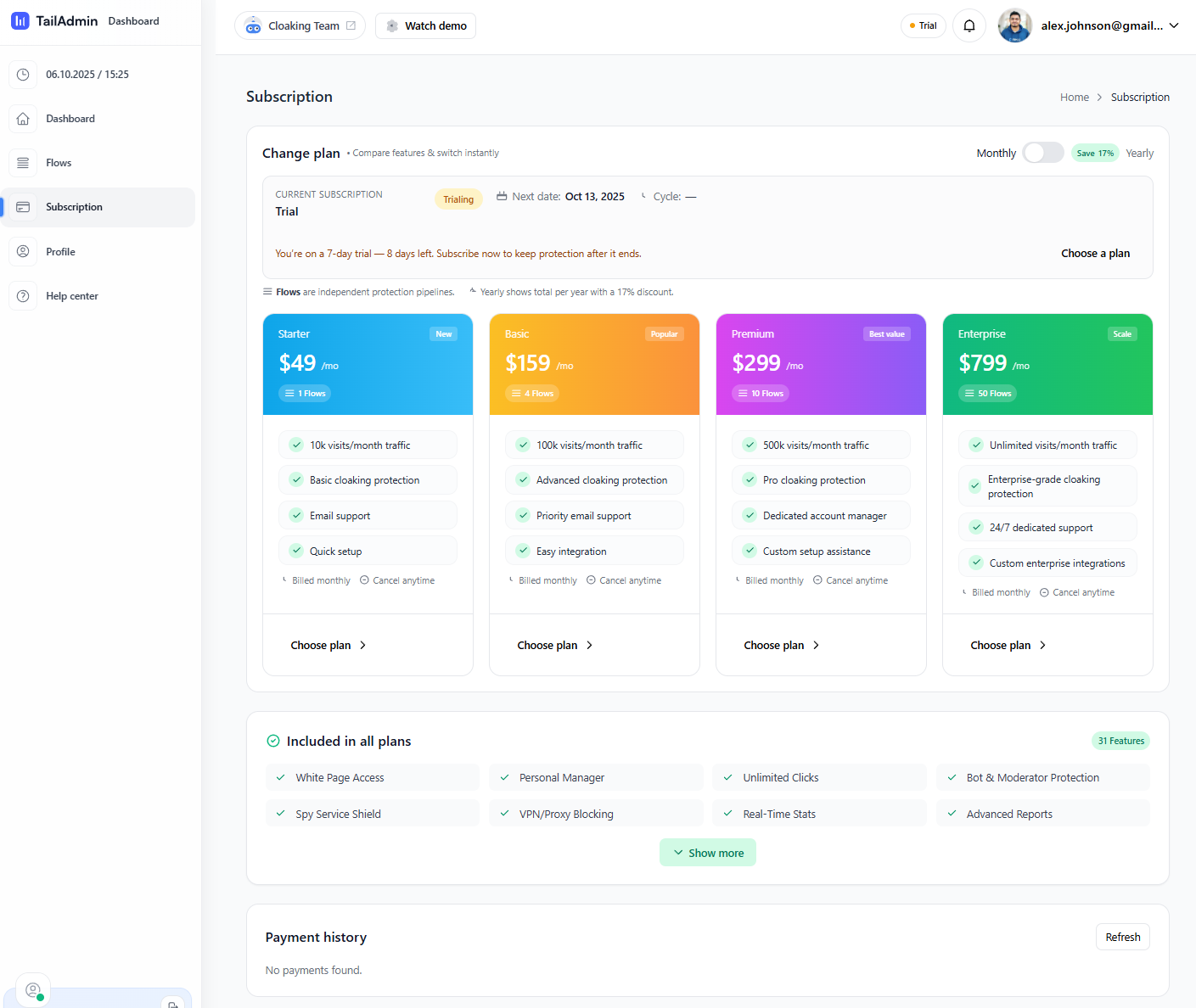
When you’re ready (or the trial ends), choose a plan and activate billing.
Go to Subscription and compare plans. Starter includes 1 Flow / 10k visits/month.
Confirm billing cycle and proceed to payment.
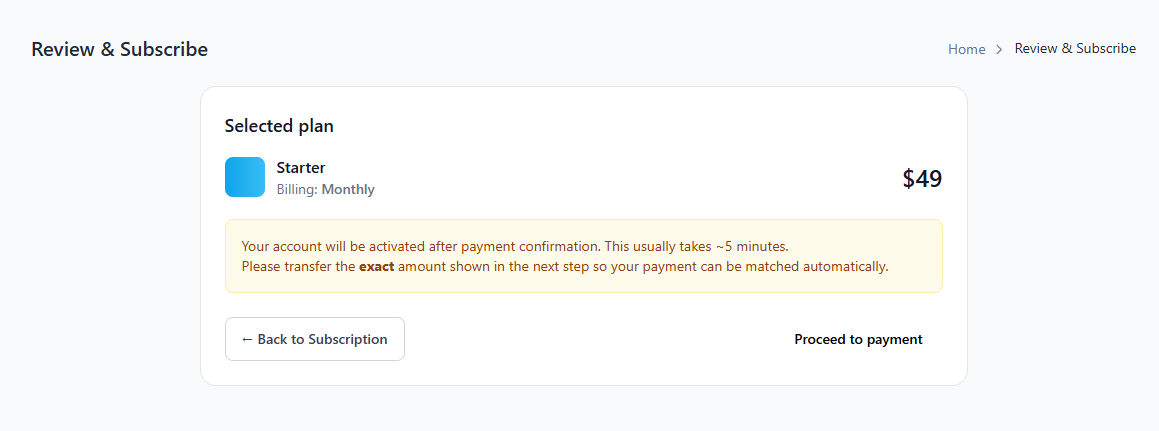
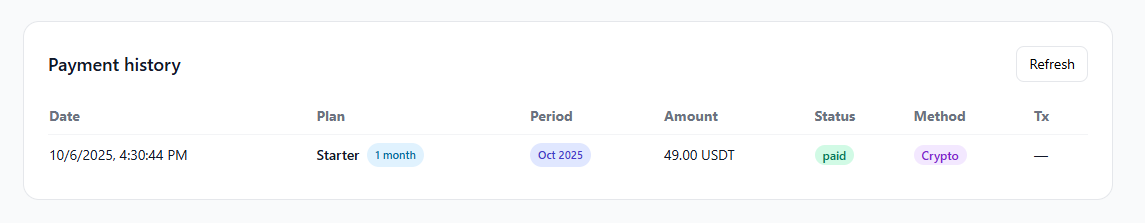
Send the exact amount to the address shown. We match automatically when the network confirms.
Go to Flows → New Flow and fill the form:
promo.example.com).Rules decide who reaches the Offer vs who goes to the White page (or gets blocked). Start conservative, then tighten.
google.com, facebook.com.gclid, utm_source; missing values send users to White/Block (per your default/other toggles).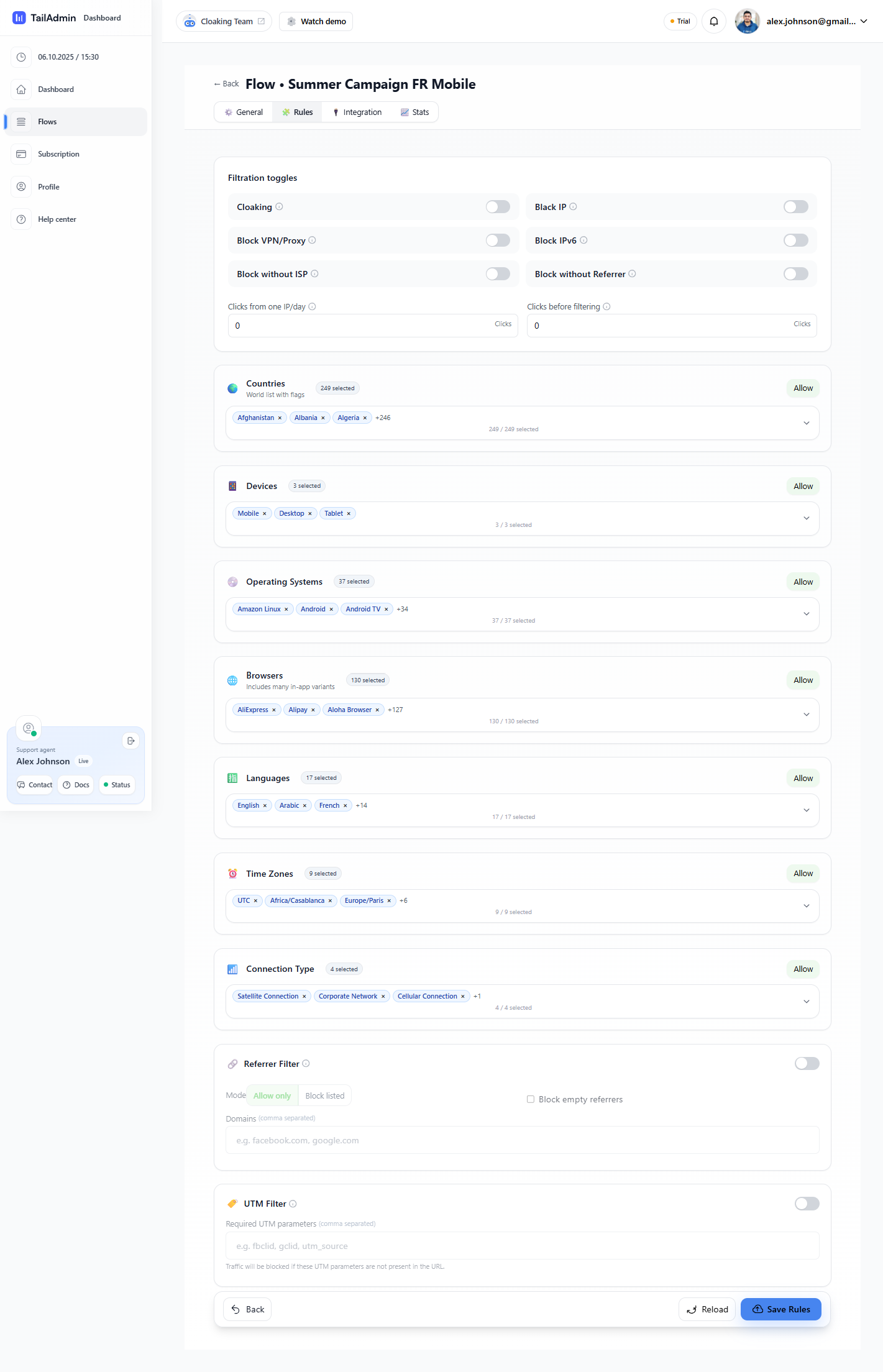
New flows start Paused. Toggle to Active, then watch Hits, Filtered, and Ratio in the flows list.
Protect pages by checking visitors before rendering your offer. Typical order:
/api/v1/check-visitor with IP, UA, headers, and path.<?php
// Laravel example (Server-side)
$resp = Http::withToken(env('CM_API_KEY'))
->post('https://api.example.com/api/v1/check-visitor', [
'ip' => request()->ip(),
'user_agent' => request()->userAgent(),
'headers' => [
'accept-language' => request()->header('accept-language'),
'x-forwarded-for' => request()->header('x-forwarded-for'),
],
'path' => request()->path(),
'referrer' => request()->headers->get('referer'),
]);
$data = $resp->json();
switch ($data['decision'] ?? 'allow') {
case 'allow':
// render offer
break;
case 'challenge':
// lightweight challenge page or fallback
break;
default:
// route to White URL
}
// Client hint (optional, never rely on client-only)
(function(){
window.cm = window.cm || {};
cm.hints = {
tz: Intl.DateTimeFormat().resolvedOptions().timeZone,
lang: navigator.language,
dpr: window.devicePixelRatio || 1
};
})();
POST /api/v1/events to improve quality scoring and reporting./api/v1/check-visitor before rendering.# Example curl
curl -X POST https://api.example.com/api/v1/check-visitor \
-H "Authorization: Bearer <API_KEY>" \
-H "Content-Type: application/json" \
-d '{
"ip":"203.0.113.12",
"user_agent":"Mozilla/5.0 ...",
"headers":{"accept-language":"en-US,en;q=0.9"},
"path":"/landing",
"referrer":"https://example.com/ad"
}'
{
"request_id": "req_9R7k1...",
"decision": "allow",
"signals": {"vpn": false,"proxy": false,"automation": false,"risk_score": 7},
"ttl": 300
}
Authenticate using a Bearer token in the Authorization header. Rotate keys regularly and store in server-side secrets.
POST /api/v1/check-visitor — real-time decision.POST /api/v1/bulk-check — batch (≤100).GET /api/v1/decisions/{request_id} — retrieve decision.POST /api/v1/events — post-conversion/quality events.POST /webhooks/traffic
{
"type":"decision.created",
"id":"wh_abc123",
"created":1738531200,
"data":{"request_id":"req_9R7k1","decision":"challenge","signals":{"vpn":true,"risk_score":82}},
"signature":"t=...,v1=..."
}
CM-SANDBOX: true header to avoid skewing production.request_id to debug.600 req/min/project (burst 1200).Retry-After.401 invalid key, 400 malformed body, 422 missing fields.Some jurisdictions require consent for non-essential identifiers. See our Privacy Policy and Cookie Policy. Configure consent mode to restrict analytics until consent.
Email Contact@BestCloaking.com or use dashboard chat (24/7). For SLA, see your plan.
We’ll help you integrate Best Cloaking in minutes.
Choose which cookies to allow. You can change this anytime.
Choose which cookies to allow. You can change this anytime.